Prevent cyberattacks to protect sensitive business data.
Is your data safe from cyberattacks? Do you have any measures in place to prevent cyberattacks? How big is the impact of cyberattacks on businesses similar to yours?
These are some common questions you will face as a small business owner planning for enterprise security. Cyberattacks on small and midsize businesses (SMBs) increased by 424% in 2020 alone, and this number is escalating further due to the COVID-19 pandemic.
This shows that your small business could be well under the threat of cyberattacks. And since prevention is better than cure, adopting preventive measures right now will protect your business from breaches in the future and cut the resulting loss, if any.
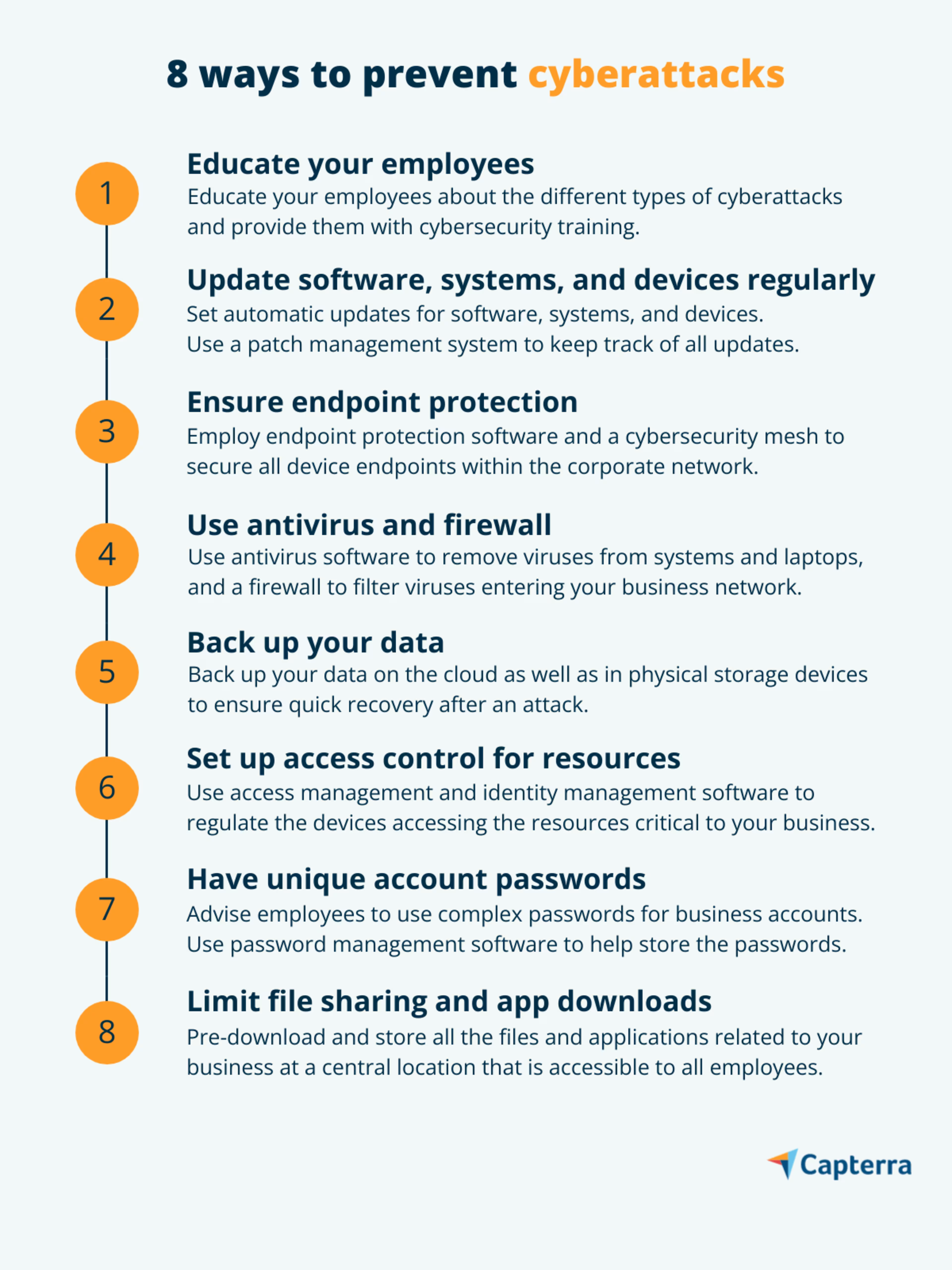
In this article, we’ve put together eight simple ways your small business can prevent cyberattacks. But before we begin, let’s first understand what a cyberattack is.
what is a cyberattack?
A cyberattack is an unauthorized attempt to gain access to a computer system, resource, or device within a corporate network. Cybercriminals use different methods, such as malware, phishing, and ransomware, to launch an attack.
A hacker could send an email asking for bank details, suggest a software download, request a donation, etc. If the target takes action on any of these, the hacker steals the information stored in the device being used or restricts user access to it.
If you don’t have a security mechanism to deal with such cyberthreats, you could be at risk such as loss of money (e.g., ransom payments, fraudulent transfers) or compromise of confidential data (e.g., patents, business secrets, research, and development). Severe cyberattacks can even result in permanent business shut down.
To help avoid such threats to your business, we suggest eight simple ways to prevent cyberattacks. These tips don’t necessarily involve buying new technology, and most are focused on staff awareness and internal controls.
Find providers that can help with your business needs by using our lists of IT services agencies by location.
1. Educate your employees on cybersecurity
Lack of cybersecurity awareness among employees is one of the major reasons for cyberattacks. When your employees are not aware of how cyberattacks are launched, what is being attacked, and how to identify an attack attempt, they are more likely to make mistakes such as downloading a virus-infected file.
To avoid these costly mistakes, educate your employees on cybersecurity. This will help them proactively identify an attack attempt and take the right preventive measures to cut the loss.
Consider training your employees on the following topics:
Password and authentication: Tips to set strong security codes and passwords, and the benefits of multi-factor authentication.
Mobile device security: Ways of protecting mobile devices containing sensitive data from malicious apps.
Social media privacy: Privacy controls on social media to prevent account hacking.
Secure behavior in remote working: Safe remote working practices to prevent data breaches.
Use of the internet and email: Ways to identify suspicious emails, websites, and ads.
Recommendations for security awareness training
Start awareness training during onboarding. Don’t wait for an incident to take place. Instead, train your employees right from the beginning—before they get access to the systems and resources critical to your business.
Consider experiential learning. Stay away from long theoretical sessions, as they can be boring. Try making the training more experience- and observation-based to generate learners’ interest. Also, consider using security awareness training software for the task.
2. Update software, systems, and devices regularly
Developers encrypt their software, operating systems, and devices with security codes (aligned with the latest security trends) to prevent unauthorized access. You should regularly update them, as outdated security mechanisms are more prone to cyberattacks.
Attackers are always looking for weak links in the security system, and missing out on a security update can allow them to launch an attack. With outdated mechanisms, it gets easy for attackers to eavesdrop or hack a software program or system and steal information.
If managing updates for multiple systems seems like a challenge, here are some suggestions to help get through:
Invest in a patch management system to keep track of all your software and system updates. Here are some free tools to try out.
Turn on automatic updates for all software platforms, systems, devices, and web browsers.
Keep your web browser plugins, such as Flash and Java, up to date.
3. Ensure endpoint security
An endpoint refers to any device (mobile, desktop, laptop, or smartphone) that sends or receives information within your corporate network. Encrypting endpoint devices using security codes is called endpoint security. You cannot manually secure devices, but endpoint protection software can do it for you.
The software encrypts your devices using a secret code or key to protect them from unauthorized access. This adds an extra layer of security, as attackers cannot decode the secret code or key to gain unauthorized access.
You can also use a cybersecurity mesh, which is a similar defense technique that independently secures each of the devices within your corporate network. It creates individual security parameters at each access point, and all access points are managed by your security and risk team.
A cybersecurity mesh is suitable for a remote work environment where resources and systems are accessed by employees using various devices from different locations. It enforces a strict user verification and authentication process to allow access, thereby ensuring better data security.
Source: Gartner’s Top Strategic Technology Trends for 2022 (full report available to clients)
4. Use antivirus and firewall
Antivirus and firewall are among the most common cyberattack prevention methods to strengthen your company’s security mechanism. Use antivirus software to detect and remove viruses from your business computers and laptops.
Top it up with firewall software to monitor and filter viruses trying to enter your devices or business network. Firewall is a network security technique that blocks unauthorized entry attempts, preventing an attack at an early stage. Most operating systems such as Mac and Windows have their own firewalls—Windows Firewall and Mac Firewall.
5. Back up your data
Data backup is among the most neglected aspects of cybersecurity. Its negligence can result in resource or financial loss to your business. Therefore, always back up information that is critical to your business—online (cloud storage) as well as offline (hard disk or computer memory).
Instruct your employees to make data backup a habit. Doing this will help restore any lost information and ensure a smooth flow of work if ever your business becomes a victim of a cyberattack.
Here are some tips to manage the data backup process:
Use data backup software.
Back up your data at multiple storage platforms and different cloud vendors.
Turn on automatic data backup for systems and resources.
Always encrypt your data storage platforms with a security code.
Stay aware of the data recovery time for the platforms you use. This is beneficial post-attack.
6. Set up access control for resources
Your business must have an inventory of resources—each useful to a specific stakeholder and shared accordingly. For instance, your HR partner does not need information related to legal compliance. That information is your legal team’s concern and should be limited to them. Similarly, share only relevant business resources with your employees or teams.
We recommend using access management software and identity management software to regulate and track how information is shared with your employees. Create a defined list of authorized users who can access the systems and resources. The software will send you a notification in case of an unauthorized access attempt, and you can immediately change/update the user rights to prevent a security breach.
7. Have unique account passwords
Simple login passwords can be easily guessed by attackers. Plus, most employees reuse their passwords for multiple business accounts, making all accounts vulnerable to hackers. Research suggests that 91% of people know that reusing a password for multiple accounts is a security risk, yet 66% continue to do so anyway.
Advise your employees to keep unique and complex login passwords for accounts and resources carrying sensitive information. Having a unique combination of letters and numbers in passwords and changing passwords at regular intervals will help enhance business security.
Remembering multiple passwords can be challenging for your employees. Provide them with password management software to record multiple passwords and recall them when needed.
Tips to enhance login security
Strengthen your security mechanism with multi-factor authentication, a technology that uses a security key or push notification, in addition to a username and password, to validate the identity of a user trying to gain access. It helps prevent any identity theft and ensures only authorized users get access to your business systems and resources.
8. Limit file sharing and app downloads
File sharing and application downloads are among the most common activities on the internet. Therefore, they are prime targets for cybercriminals to plant a virus. To prevent your systems and resources from getting exposed to malicious elements, such as viruses, via these activities, limit/restrict them for your employees.
Block sharing and downloading of files and applications via external sources, such as web browsers. Instead, make them available on internal platforms such as private cloud storage. You can also pre-download and store all the required files and apps in a centralized location that is accessible to all employees.
We suggest using cloud storage software and team collaboration software to facilitate secure file sharing and downloading for your employees. Also, educate your staff on how to identify a phishing attack, as most of these attacks are launched through file download links.
Strengthen cybersecurity for your small business
Now that you know the different ways to protect your small business from a cyber attack, what should you do next? Start by learning how to build a cybersecurity incident response plan that helps manage data breaches and mitigate loss.
Here are some additional Capterra resources on how small businesses like yours are dealing with cyber attacks:
