Chances are you have logged into something through single sign-on in the last week, but do you understand how it works and why your business should use it?

What's the most valuable part of your website?
Your sweet algorithm for compressing video files? Your ever-growing collection of original IP? Or, maybe the gaming experience your users get as they hack their way through a place that is basically Middle Earth but that—for legal reasons—is definitely not Middle Earth?
From a hacker's perspective, none of that matters. Hackers are looking for personal data. Names, addresses, emails, and passwords—details about a user’s identity that can later be used for phishing scams, ransomware attacks, and identity theft.
Passwords and other login details may top the list these days. Home design company Houzz lost over 48 million passwords last year. Zynga, the game producer known for “Words with Friends” and “Draw Something,” was also hit by a security attack, with an estimated 218 million user credentials stolen.
Unfortunately, when it comes to security breaches prevention is never 100% possible. However, there are ways to reduce the chances of users having their passwords stolen in a breach. Welcome to single sign-on, an identity management structure that solves a bagful of common business problems.
What is single sign-on (SSO)?
Single sign-on (SSO) is an identification system that allows websites to use other, trusted sites to verify users. This frees businesses from the need to hold passwords in their databases, cuts down on login troubleshooting, and decreases the damage a hack can cause.
SSO systems work as an identity provider—sort of like an ID card. For example, if you get pulled over for speeding, the police officer doesn’t have to know you personally; they can just look at your license and see that your state vouches for your identity.
Likewise, with SSO, your website doesn’t make you prove your identity by checking within itself. Instead, it checks with an SSO provider (such as LinkedIn, Microsoft, or Google) to see if it can verify your identity. If it can, the site takes their word for it.
Technically, a lot of what's being called single sign-on is actually a mix of pure SSO and delegation or federation. There's a sort of jumble between all the platforms, especially as identity-as-a-service providers get into the mix.
We'll use SSO here, with callouts when the distinctions really matter.
How does SSO work?
Explaining the system in broad strokes is simple, but explaining the process of implementing SSO requires a bit more background. Normally, when you log into a system, the service provider or domain (website.com, in this example) will authenticate you on its own. Like so:
1. As a user, you hit an intermittent page on website.com that checks to see if you're already logged in. If you are, SSO authentication is complete and the system will send you off to whatever you really wanted (your Gmail inbox, for instance).
2. If you're not already logged in, you're presented with a login screen.
3. You drop your login credentials (email and password) in the form, website.com checks those credentials against its database, and then you're either logged in or rejected.
4. If you're logged in, website.com will issue some sort of tracker. This could be on the server, or it could be sent over to you as a token.
Now, whenever you move around the site, the system just checks to make sure the tracker—and thus your authentication—is up-to-date.
If you were to do the same thing with SSO in place, it would look more like this:
1. As a user, you hit an intermittent page (an SSO portal) on website.com that checks to see if you're already logged in. If you are, it scoots you off to whatever you really wanted—your Gmail inbox, for instance.
2. If you're not already logged in, website.com presents you with options for authentication via a third-party identity provider (Google, Amazon, Facebook, etc.). You pick your provider of choice and then log in with that provider, let's say, Google.
3. Google checks to see that you're you, checks to see that website.com is the site it's claiming to be, then authenticates you based on the Google password database and issues a token back to website.com.
4. Website.com gets the token from Google, verifying your identity. It now associates you with the rest of your user data—preferences, history, shopping cart, and so on—and you're all set.
In a true SSO system, you'll just cruise around from site to site with full access.
In a delegated system, Google will return both a verification of identity and set of authorized uses. Website.com might be given access to your name and email, for instance, but not be shown your location or age. (See the example below.)
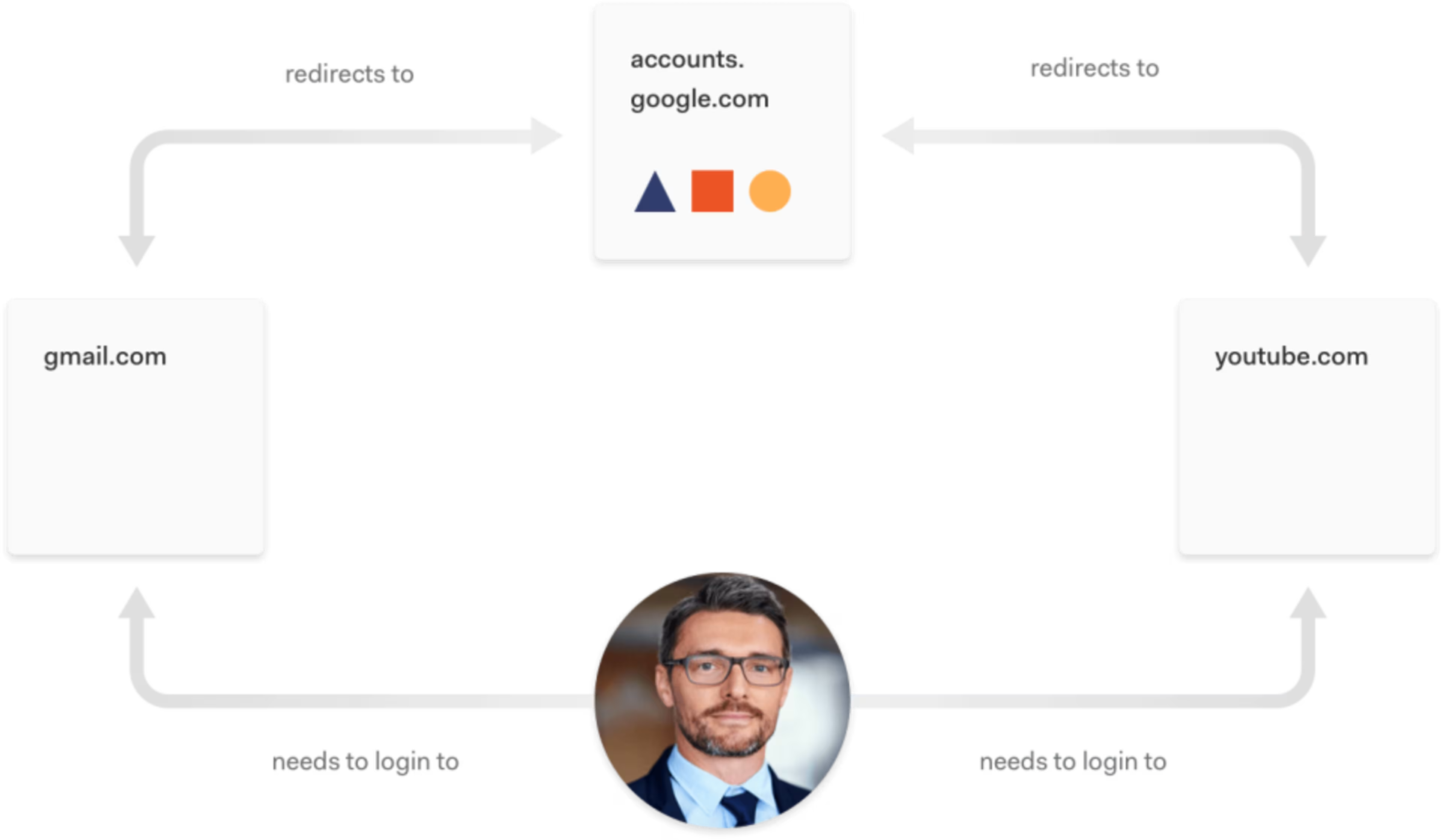
An example of the redirection flow while using SSO from Auth0 (Source)
Great! But why would anyone bother with this?
The benefits for users
There are a few main benefits for users who interact with SSO.
Convenience. Users only need to remember one set of login details. By connecting your site to their logins at Google, you ensure that even sporadic users can remember how to log in; they just log into Google.
Transparency. Users know what's being shared from one system to another—at least in a delegated system. It's like when you install a new application on your phone and it asks for permission to access your photos, contacts, and bank account. If you're not happy with those options, you can opt out.
Speed. With SSO, users don't have to go through lengthy sign-up and authorization processes. Because Google has already done all the email verification and data collection, new users can sign up as quickly as they can log into Google.
Security. Users also get the peace of mind that comes from knowing that website owner Marlon Rando doesn't have their password stored in plain text somewhere out in the internet backwater. Google continues to be the main point of trust, which allows the user to try new things without fear.
The benefits for your business
That's great news for your users, but what's in it for you, the website owner?
More user sign-ups. SSO provides a lower barrier to entry, so new customers can sign up easily and securely, by relying on a known brand. Facebook is managing the process, so they don't worry about your unknown system and brand. Trust is increased, which increases conversions.
Less work on the back end. Meaning, you won't have to futz around with passwords. While reducing your hack risk is important, even more important is not having to reset people's passwords every five minutes. All the authentication and password heavy-lifting is managed by the trusted authenticator.
Data collection. You can also tap into more of the information as Google or Facebook or whoever makes it available. It’s all the benefits of data collection without all the hassle associated with it.
Reduced risk. Finally, you're removing that tempting pie from the windowsill. Hackers have less incentive to hit your site if you don't host a ton of login details. You're also less likely to have a bunch of users with horribly weak passwords poking holes in your site's overall security.
In short, adopting an SSO solution can make life easier for you and for your clients.
SSO + MFA: Convenience without sacrificing security
SSO is convenient, but it has its pitfalls. Namely, if an SSO account is hacked, others under the same authentication system can also be targeted. One way you can counteract this risk is by implementing multi-factor authentication (MFA).
Multi-factor authentication
A user authentication method that requires users to provide two or more verification factors.
SSO combined with MFA does a much better job at protecting user accounts than SSO alone. Additionally, providing users with the efficiency and ease that MFA and SSO offer means lowering the chance of a password reset or help desk call.
Getting started
If your business is technically inclined—which is to say, you employ software engineers of some stripe—you can also check out the OAuth protocol, which underpins many of the commercial solutions on the market.
If you’re looking for a tool you can integrate with your current tech stack, you can browse Capterra’s identity management directory for a full list of SSO providers, where you can use the filtering tool (left side of the screen) to browse MFA-specific products. Our authentication software and single sign-on directories are both great places to find SSO and MFA tools.
