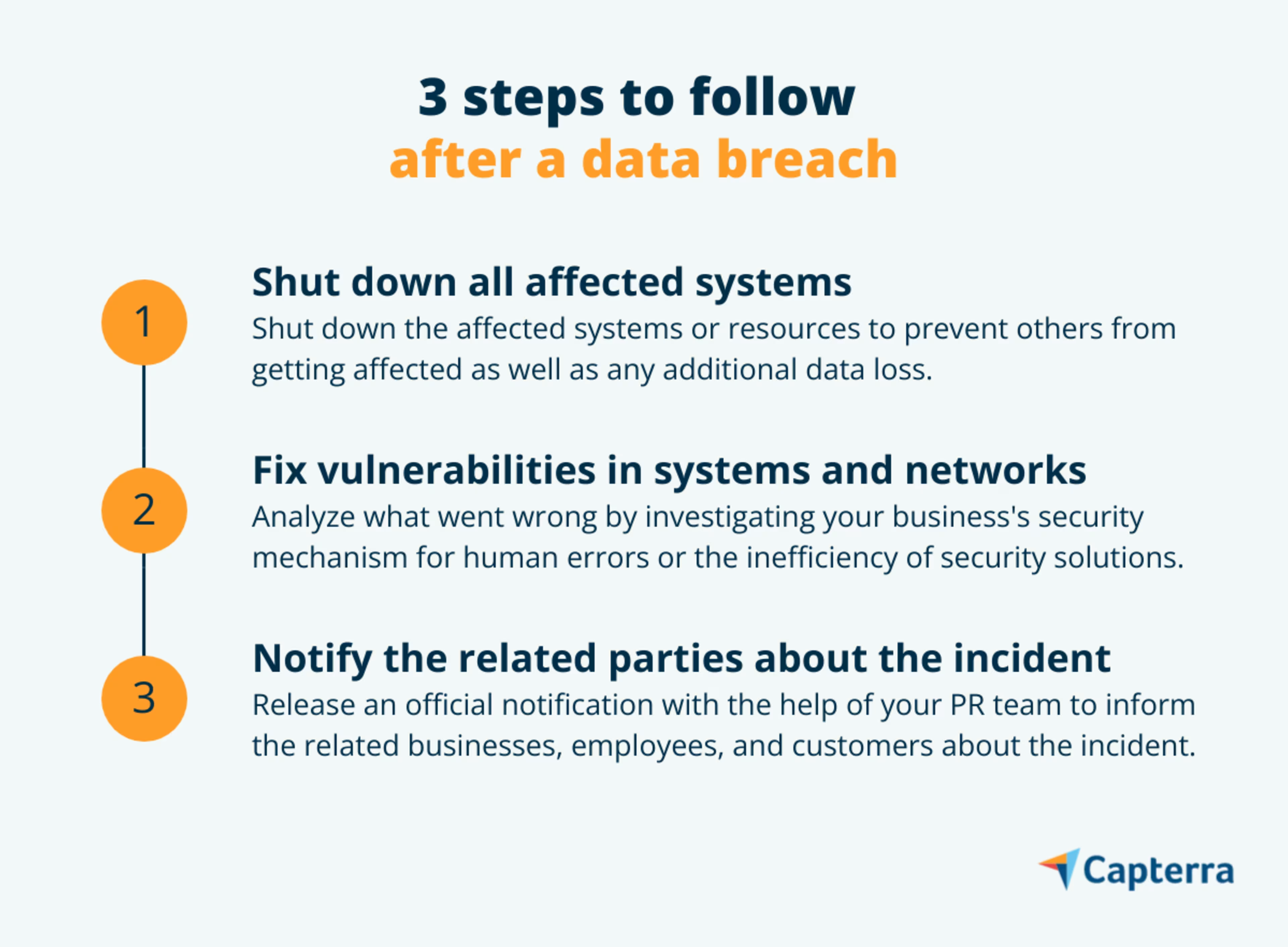
Take these three steps right after a breach incident to prevent further loss.
Operating in a digital workplace means using the internet to share and manage business resources that can be accessed online on compatible devices. But this always-on, always-connected workplace model has the potential to compromise the security of your business and make it prone to cyber-risks.
Cybercriminals are always in search of such loose ends to break into your enterprise network and steal sensitive information by bypassing the security mechanism. This process is known as a data breach.
If you’re someone responsible for IT security management at your business, you should know how to deal with a data breach一the immediate response and recovery steps to take and the stakeholders to involve for quicker resolution.
In this article, we explain the three steps you should take right after a breach incident to prevent further loss and related damages. But before we get to that, let’s first understand what a data breach is and how it impacts businesses worldwide.
What is a data breach?
A data breach or data leak is a security incident in which hackers steal or get access to confidential or sensitive data by bypassing the security mechanism. This data could be confidential business information (e.g., credit report, bank account credentials) or customer information (e.g., email addresses, social security numbers).
Hackers attempt data breaches using different types of cyberattack techniques, such as identity theft, planting a virus into a system, or tampering with the IT infrastructure to block user access to IT resources.
The impact of a data breach
Renowned sports brand Puma recently got hit by a data breach incident that impacted over 6,000 individuals, including employees and customers. The attack was launched using ransomware—i.e., holding information for money. Similarly, edtech startup Unacademy lost over 20 million user records in a data breach incident back in 2020.
These examples highlight that data breaches can impact businesses of all sizes. To limit the impact, your business should take the right data security measures after an attack—in case you face one.
Find providers that can help with your business needs by using our lists of IT services agencies by location.
Step #1: Shut down all affected systems
Start by shutting down the systems affected by the breach to prevent other systems from getting compromised. Once that’s done, change the login credentials of all business accounts and servers carrying sensitive information.
Mobilize a team of experts to identify the root cause of the security breach, its source, and if the hacker still has access to your systems. Include experts from IT security and risk, legal, forensics, operations, human resources, communications, and upper management in this team—depending on the size of your business.
While taking these security measures, be careful not to destroy any evidence from the incident; it will assist the forensic team in investigation and remediation.
Step #2: Fix the vulnerability in affected systems and networks
After isolating the affected systems, resources, or networks, identify the weak ends in your company’s security mechanism that opened the doors for the hackers. Start by investigating how your employees and clients share business information, as human errors account for the majority of data breach incidents. According to industry research, 22% of data breaches happen due to human errors.

Once you have identified the cause of the breach, run a series of network segmentation tests to identify less secure subnetworks. These tests run a port scan on your enterprise network looking for unauthorized device IP addresses. Network segmentation is validated as properly working when no unauthorized IP addresses are found.
In case a subnetwork is compromised, isolate it to prevent the entire corporate network from getting infected. Ask forensic experts to gather all the information about the unauthorized IP address or addresses through which the attack was likely launched, and prepare a data breach report to implement the recovery plan.
This report should include details about the weak ends in the network that enabled unauthorized access and the technique used by the hacker to launch the attack. The report will let you analyze how strong or poor your existing data security mechanism is as well as identify ways to strengthen it to prevent future attacks.
Step #3: Notify related parties about the breach
The last step is notifying all the stakeholders impacted by the breach. First, speak to law enforcement to identify if any federal or state laws were violated during the breach. If yes, ask them to suggest remediation steps to avoid lawsuits.
Next, make a formal media announcement stating the occurrence of the breach, the intensity of data loss, and the people (customers and employees) affected by the breach. Maintain transparency in communicating the remedial measures taken to stop the breach. This will help you regain the trust of related parties.
Consider involving a public relations (PR) team to effectively deliver the message. Also, anticipate questions that the related parties may ask about the incident. Some common questions are:
Was our personal information, such as contact and bank details, leaked?
What data protection measures were taken to mitigate the attack?
Are there any steps we can take at our end to reduce losses?
If your business operations involve collecting customers’ personal data—say, social security number, credit card number, or health information—and that data has been compromised during the breach, you should immediately inform institutions such as the bank and the local cybercrime cell. This will allow them to monitor the compromised accounts for any fraud alert or track similar complaints from customers.
Strengthen IT security to prevent data breaches
A data breach can be crippling to your business. The average U.S. company loses about $8.2 million due to data breaches, according to a Gartner report (full research available to Gartner clients).
Implementing a cybersecurity incident response plan can lead to effective recovery. Use the plan to monitor your systems, detect security incidents, and implement prevention or recovery methods to reduce the resulting loss. You can also use software tools to strengthen your company’s security posture and prevent attacks in the future.
Software solutions to secure your business from data breaches:
Data loss prevention software provides visibility into data usage across your business and ensures compliance with policies and regulations to address threats such as exposure of sensitive data or accidental data loss.
Network security software, paired with a firewall, constantly monitors the network traffic to identify intrusion attempts and notifies suspicious events to the IT security team for further investigation.
Endpoint detection and response (EDR) software continuously monitors, investigates, and responds to active threats that target network endpoints. It helps identify potentially harmful applications and new malware in real time.
Multifactor authentication software secures the credentials of your business accounts to prevent identity theft attempts.
Security awareness training software educates your employees on how to identify cyberattacks, take preventive data protection measures, and effectively recover from the loss.
Still curious? Explore Capterra articles on cybersecurity and IT management.
